Beyond Identity
Designing Secure Authentication
Lead Product Designer • 2025 • B2B, Desktop/Mobile Web
Overview
Highly regulated, enterprise customers had unique authentication use cases
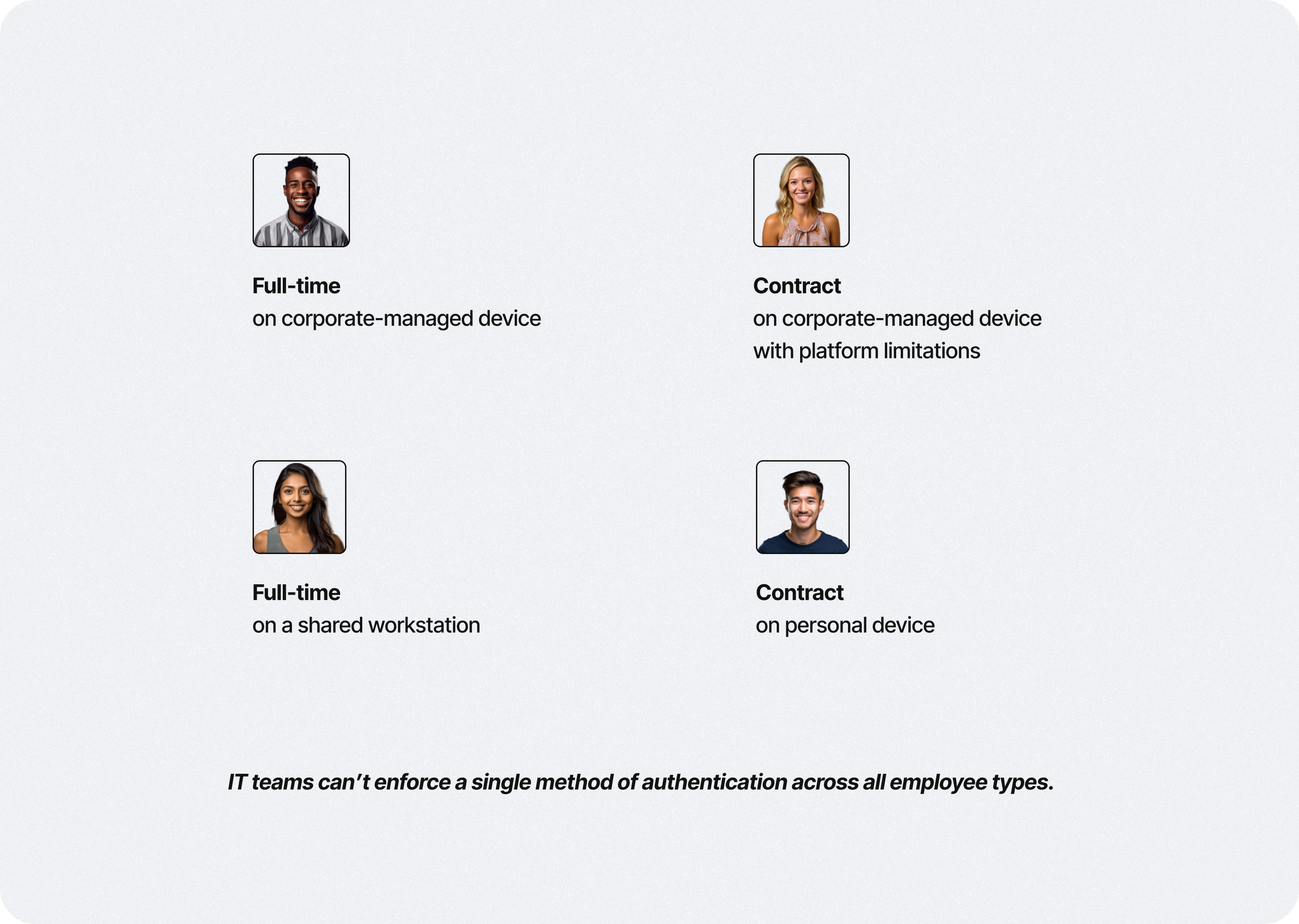
Different employees authenticated in different ways depending on their status (full-time/contractor), type of device, type of resource they’re accessing, and personal preference.
These companies couldn’t enforce a single way to authenticate across all employees, so they required configurability to accommodate different needs they had.
Impact
This helped address core needs for some of our key customers
PROBLEM
Companies didn’t have enough flexibility in authentication options
Although IT teams could mandate the use of Beyond Identity for employees on company-owned devices, they couldn’t do that with employees on personal devices or company-owned devices using platforms that Beyond Identity didn’t support. Some employees were just exempt from logging in a specific way due to the company’s own needs.
Users
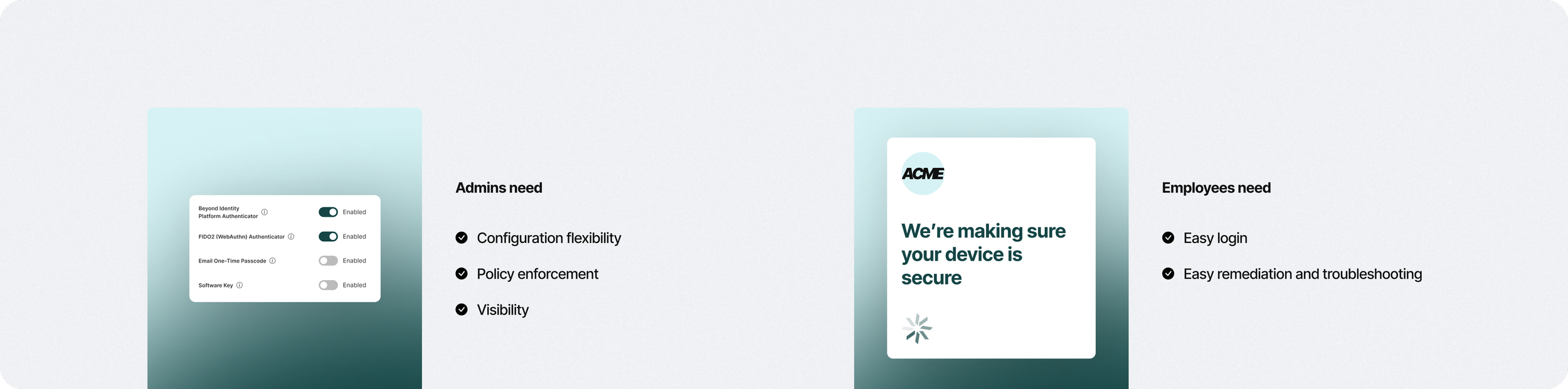
Admins needed configurability and visibility, and employees needed flexibility and seamless UX
There were IT and security admins that needed to be able to configure different authentication methods, policy to enforce these different methods, and the visibility to manage activity and address compliance requirements.
Employees needed clarity in what methods they were allowed to log in with and simplicity in enrolling in these different methods. The main goal was making sure employees could successfully authenticate and self-remediate if they have issues as much as they can.
Designs
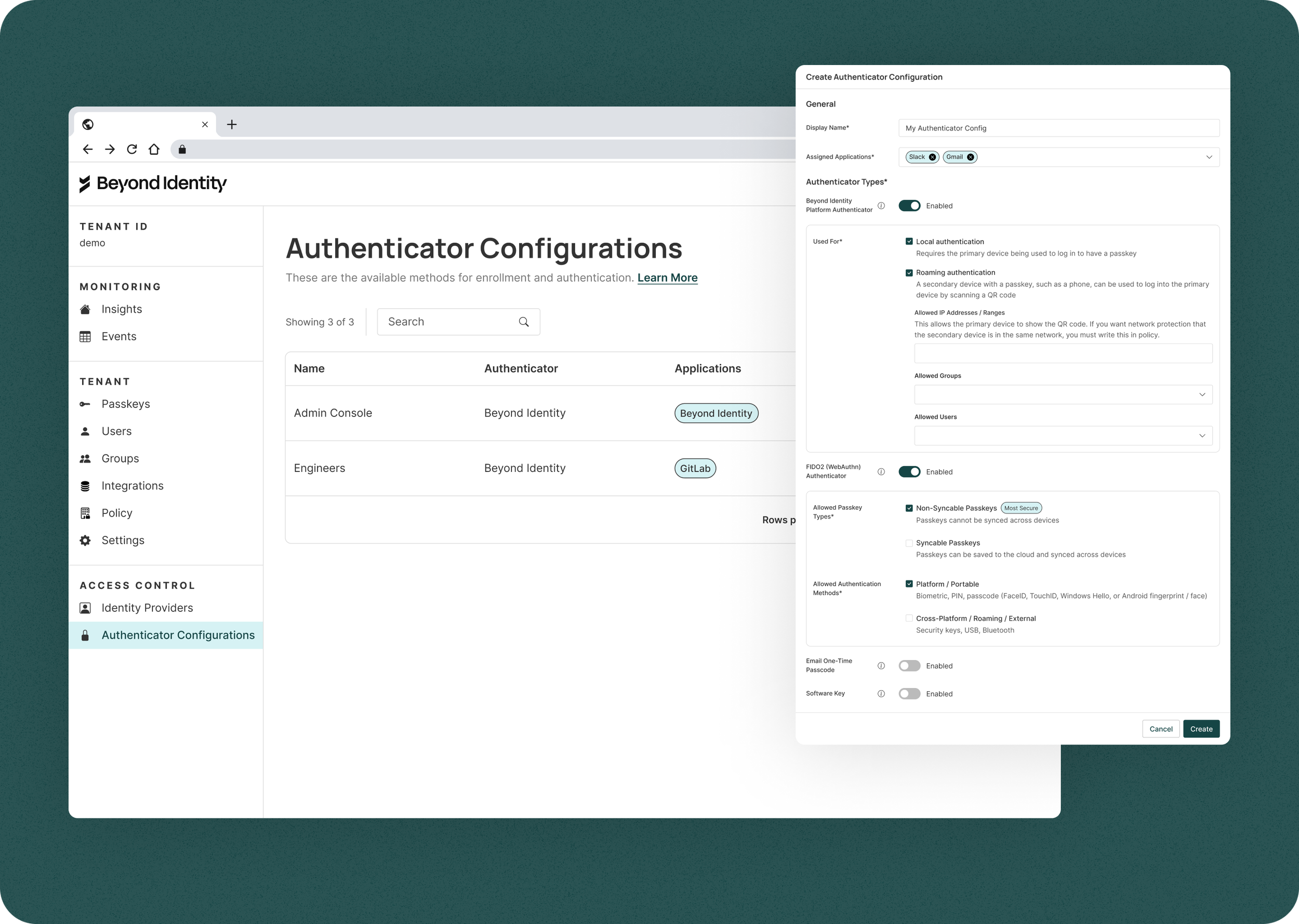
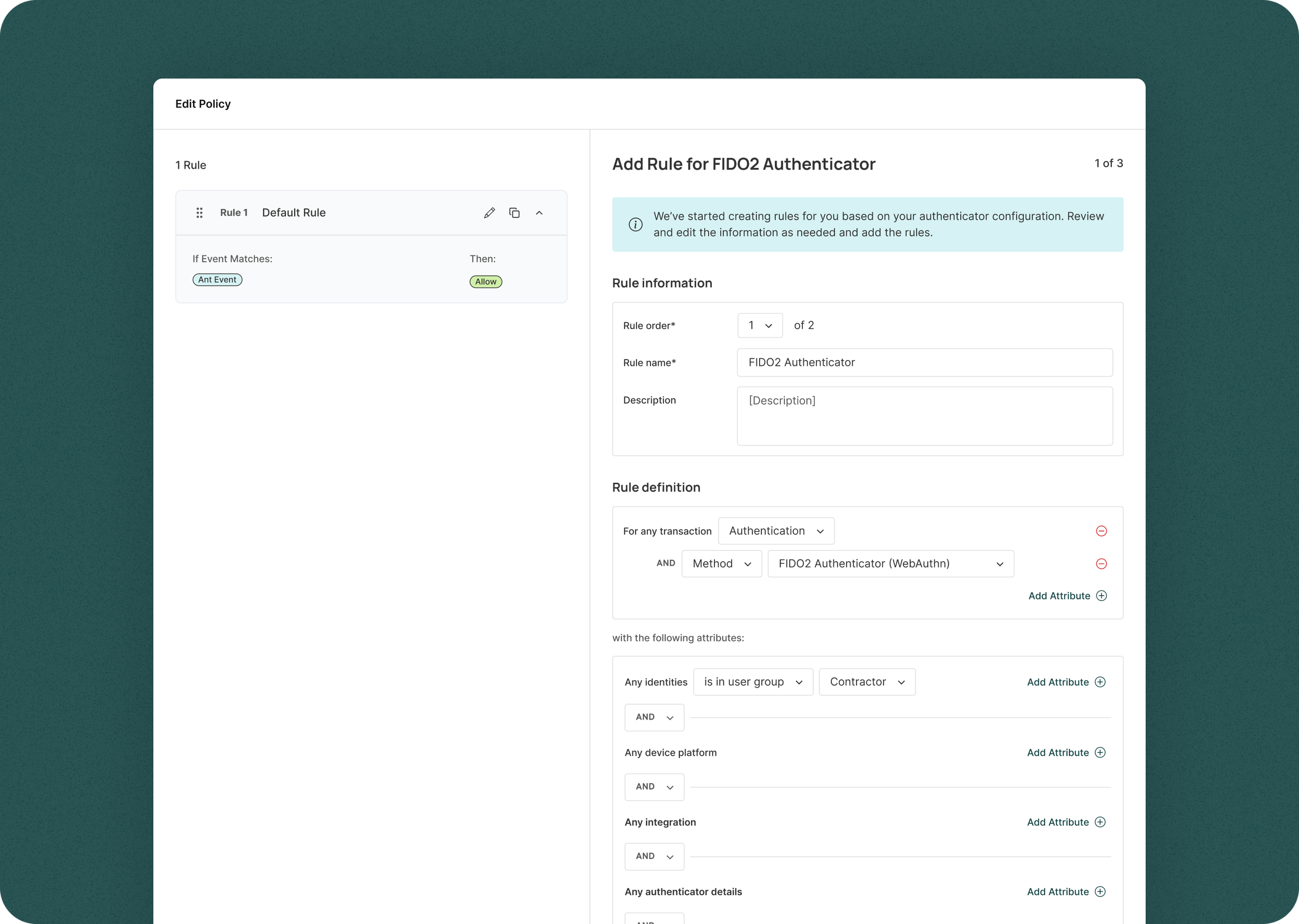
Flexible and Simple Admin Configuration
Admins needed a way to configure different authentication methods and many were specifically interested in implementing FIDO2 passkeys, a secure browser-based passwordless authentication solution.
In its most ideal form, it addresses both the security and seamless user experience needs customers had, but there were platform-specific limitations that made implementation difficult.
My goal was to provide flexibility in configuration to allow admins to configure a more security-focused or more user experience-focused FIDO2 solution depending on the company’s risk profile.
Designs
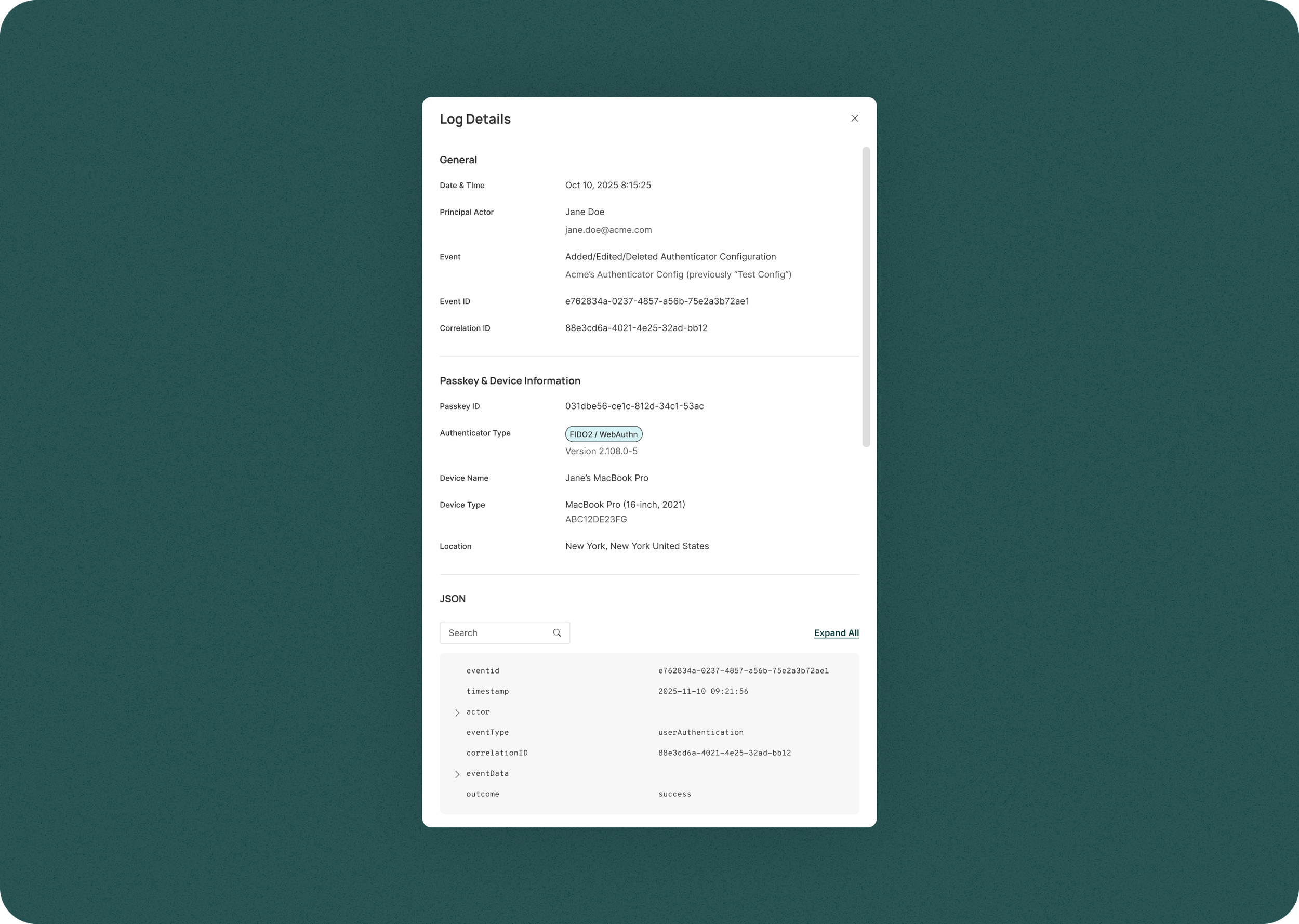
Admin Visibility
Admins needed to a way to see and manage authentication methods users enrolled in and authenticated with. This was needed to troubleshoot any issues, revoke access if needed, and provide documentation for compliance purposes. With the introduction of a new method to log in, we needed to expand on our table component to address these new needs.
design
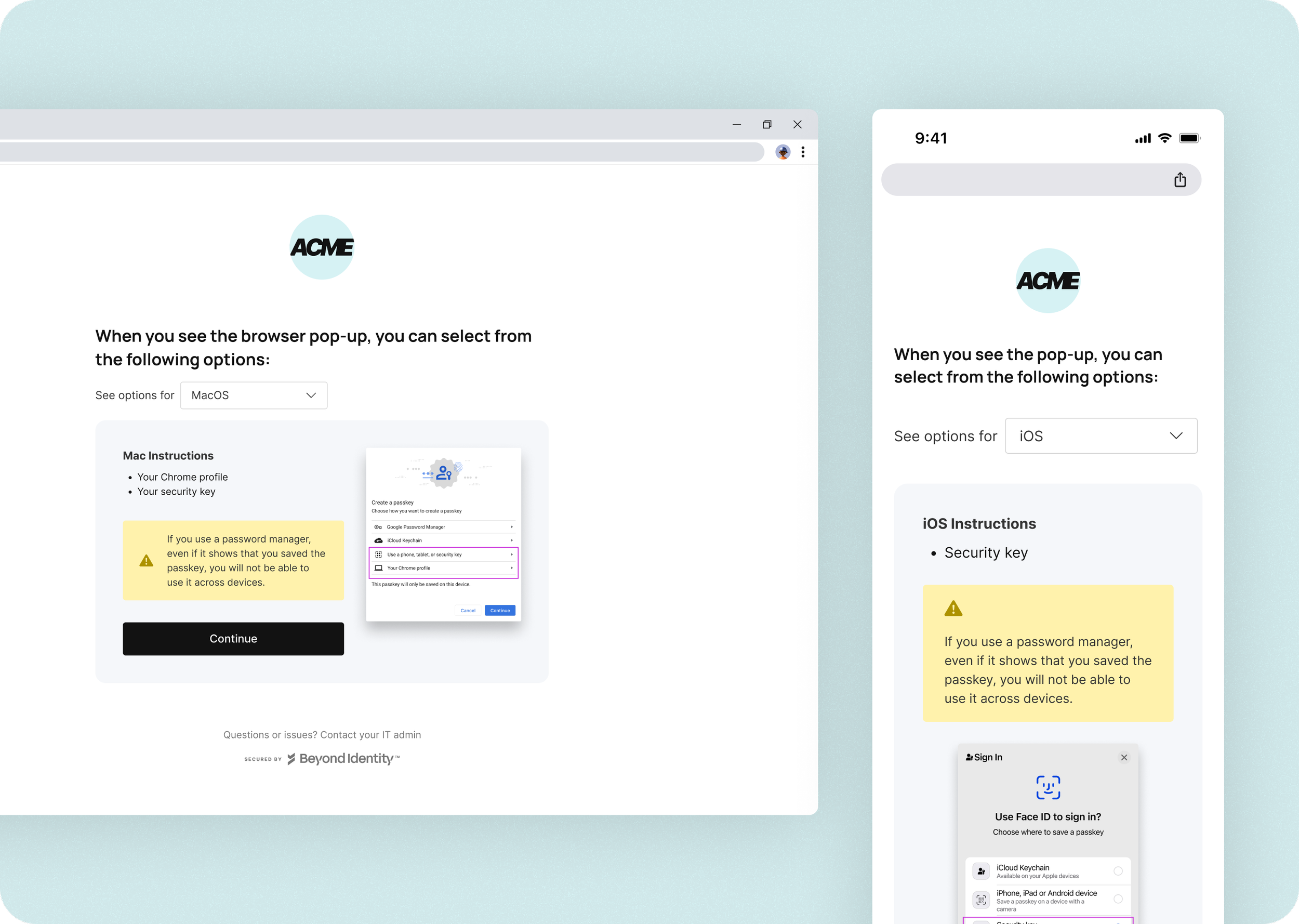
Seamless End User Enrollment
An employee’s main goal is to be able to easily log in so they can focus on their work. To an employee, logging in is a small part of their day and if the experience is done right, it should almost be invisible. The problem is that when issues arise, it can severely disrupt the employee’s day and cause frustration to both the employee and the IT team that’s troubleshooting.
My goal was to make enrollment of different authentication methods as seamless as possible. I worked closely with engineering and security experts to design around the platform limitations.
Design
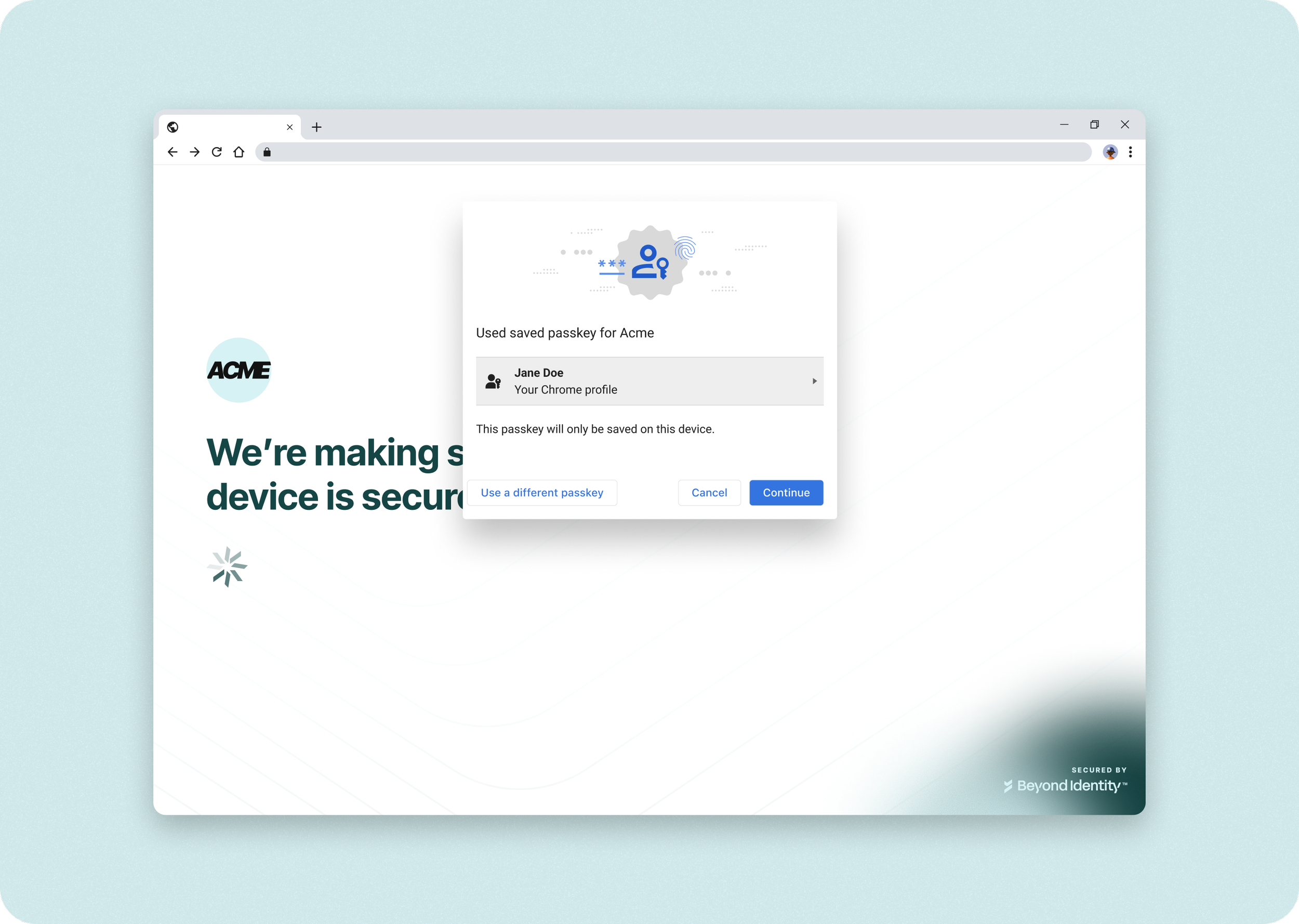
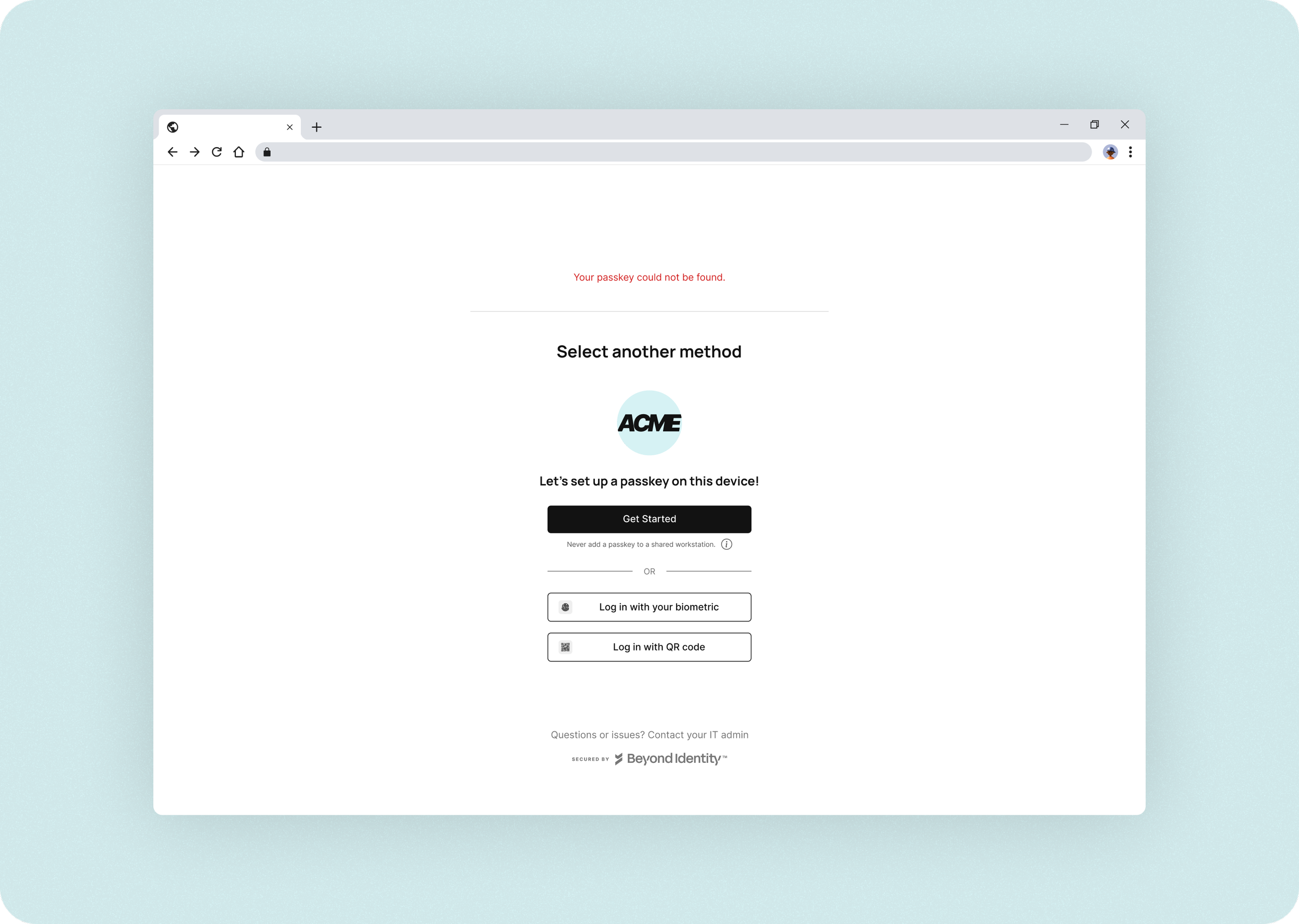
End User Authentication and Remediation
When employees run into login issues, they often quickly turned to IT for help because they didn’t know how to troubleshoot, but we’ve empowered users to self-remediate with login and account issues. I also designed notifications for users, so they’re alerted on critical activity.
learning
Challenges with Designing for Both Security & UX
The biggest challenge with designing this solution was understanding the technology – the team needed to untangle the platform-specific differences and keep up with changes in the spec in order to be flexible enough to address customer’s varying security needs. Ultimately though this became our superpower and made our solution compelling to complex and compliance-driven industries like Fintech.